Share and Follow

The Justice Department and the FBI announced they have dismantled a Russian military intelligence network that was covertly operating within the United States. This network, which had compromised internet routers, was being used to intercept sensitive information. The operation was carried out following a court order and aimed at protecting national security.
Linked to the notorious GRU Unit 26165—also known as APT28—the network exploited vulnerabilities in commonly used routers by altering their settings. This allowed the operators to redirect internet traffic through their own controlled infrastructure. Instead of hacking individual computers, the attackers seized control of routers, positioning themselves to monitor and potentially extract valuable data as it traversed the network.
In particular, the network targeted individuals by returning fraudulent DNS records. These records impersonated legitimate login portals, such as Microsoft Outlook Web Access, in a bid to capture passwords, authentication tokens, and email information from unsuspecting users.
The breadth of the operation necessitated a direct and robust response from the FBI. Officials underscored the urgency of the situation, noting that the scale and sophistication of the network’s operations required immediate intervention.
Through the court-sanctioned operation, authorities were able to confirm how the network functioned while carefully avoiding the collection of personal user content. The campaign’s roots trace back to at least 2024 when actors associated with the GRU began exploiting routers found in small offices and home offices. These devices were often neglected in terms of updates or had reached the end of their support lifecycle, making them prime targets for exploitation.
Today the FBI and @TheJusticeDept announced Operation Masquerade, a court-authorized technical disruption of Russian GRU infrastructure used to steal government, military, and critical infrastructure information.
Since at least 2024, a cyber unit within Russian military… pic.twitter.com/r8LWbZrfQs
— FBI Cyber Division (@FBICyberDiv) April 7, 2026
“Cyber actors linked to Russian military intelligence conducted a DNS hijacking campaign. These actors compromised routers and redirected traffic from connected devices to GRU-controlled infrastructure… The GRU compromised a vast number of household routers in the U.S. and around the world, as well as those used by small and medium-sized businesses to access high-value intelligence targets.
Given the scale of this campaign, we needed to act. The FBI developed and executed a court-authorized technical operation to harden compromised routers across the United States… Commands reverted manipulated DNS settings, collected evidence, cut off GRU access to compromised U.S. devices, and prevented re-exploitation.”
Officials said the court-approved commands confirmed how the network operated while avoiding the collection of user content, and the campaign dates back to at least 2024, when GRU-linked actors began exploiting small office and home office routers, often targeting devices that had not been updated or were no longer supported.
Investigators said the actors first compromised routers at scale, then filtered traffic moving through those devices to identify government, military, and infrastructure targets.
That filtering narrowed the operation from broad access to targeted collection without direct control of the end device.
“Without FBI intervention, the GRU would have continued intercepting encrypted traffic and stealing sensitive information, including emails, passwords, and authentication tokens… Russia’s cyber program is an enduring threat, and the FBI works with our partners every day to disrupt their operations and support victims across the country.”
The operation did not involve seizing devices, and users can reverse the changes by restoring factory settings or manually resetting the router’s configuration.
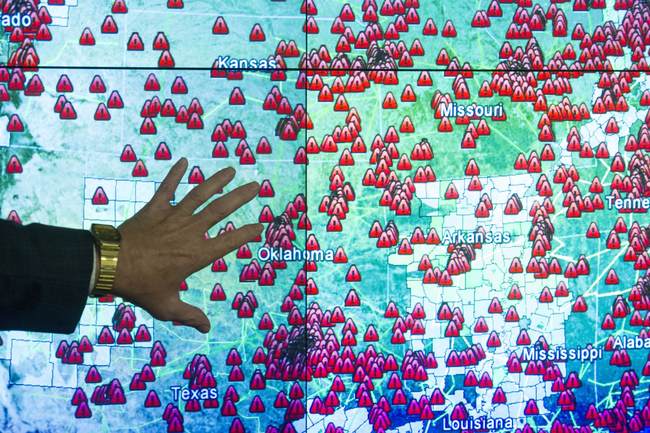
Compromised routers were identified in at least 23 states, part of a network that extended beyond the United States and supported a broader intelligence effort.
“The GRU’s predatory use of networks in American homes and businesses for its malicious cyber operations remains a serious and persistent threat… we will continue to use every tool at our disposal to detect such intrusions and expel hostile foreign actors from our nation’s networks.”
Alongside the disruption, federal agencies released guidance outlining how the campaign worked and what steps users should take to secure their devices. The DOJ says the fixes are basic and tied to how the intrusion worked: Update firmware, verify DNS settings, disable remote access where it is not needed, and replace unsupported devices.
That focus on routers is not new. Federal regulators have warned that compromised network hardware can serve as an entry point into larger systems, including campaigns targeting U.S. infrastructure, because routers sit between users and the internet and handle traffic for every connected device on a network.
The FBI cut off that access inside the United States, removing the pathway the GRU relied on to move traffic through compromised routers.
Any router left unpatched can still be used the same way.
Editor’s Note: Do you enjoy RedState’s conservative reporting that takes on the radical left and woke media? Support our work so that we can continue to bring you the truth.